Where possibilities
begin
Gain new perspectives for your digital transformation. You can follow the blogs on this page to get latest information.
Version Control That Holds Up in Due Diligence: 10 Naming and Versioning Rules Partners Can Enforce
Due diligence is a pressure test. Multiple firms, multiple workstreams, thousands of sensitive files moving fast. And regulators, investors, and internal audit teams may later ask: Which version was relied on, who changed it, when, and why?
Version control isn’t administrative overhead. It’s part of your defensibility. The goal is simple: every stakeholder can find the correct document iteration fast, and you can prove the integrity of the document history through audit trails.
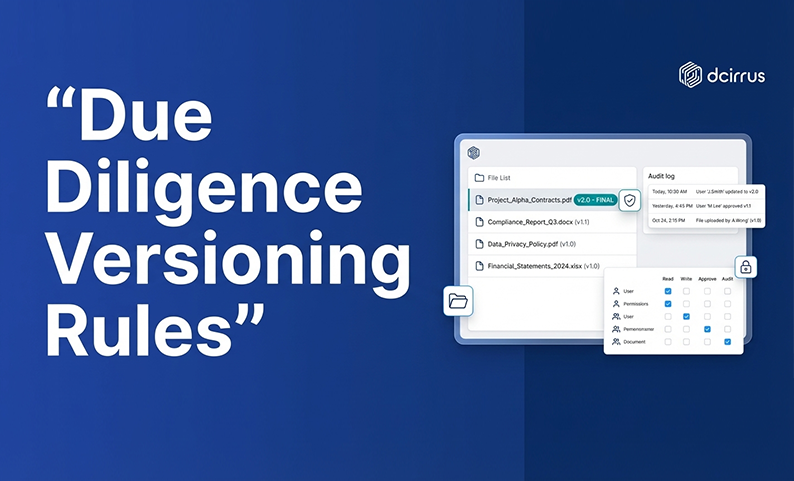
Modern virtual data rooms help by combining secure repository controls with role-based permissions, version history, and audit logs (so rules aren’t just written down, they’re enforceable).
What is version control and why does it matter in regulated transactions?
Version control in due diligence controls confusion and risk. When partners share drafts through email threads, ad hoc cloud folders, and overlapping edits, the “latest version” becomes a debate. Right when timelines are tight and stakes are high.
Strong versioning reduces rework and speeds review cycles. More importantly, it creates a traceable chain of custody: how a document evolved, who had access, what was approved.
In a transaction context, version control means you can:
- Track each revision of a document across its lifecycle
- Prevent accidental overwrites of critical files
- Identify which version is current, draft, or final
- Produce a defensible history if regulators or counterparties challenge a disclosure
This matters because due diligence is a regulated workflow, not just collaboration. Whether you’re preparing for an IPO, M&A review, or financing round, document control supports records management and regulatory adherence.
Common mistakes with version control in multi-party due diligence
Most version-control breakdowns come from predictable friction points:
- Too many contributors editing the same document in parallel
- Inconsistent file naming across different firms
- “Final” files that later get edited and re-uploaded as another “final”
- Redacted versions mixed with revised versions without clear labeling
- No shared method to record what changed between drafts
- Weak access control (too many users can upload or replace documents)
- Poor visibility into who viewed, downloaded, or altered a document
These issues create audit exposure and slow transactions. Teams spend hours reconciling discrepancies.
Why naming and versioning rules support audit readiness and compliance
A naming convention is the simplest control that scales across organizations. It’s also one of the easiest to enforce if you agree on the rules early and implement them inside the systems partners actually use.
Audit readiness comes from three things working together: consistent naming and version numbering, permission controls, and audit trails that record actions and preserve history.
For CFO-led teams, the same discipline helps reduce due diligence documentation friction like inconsistent categorization, high document volume, and version control gaps.
Compliance drivers: SEBI and other regulatory expectations
In regulated transactions, assume documentation may be reviewed after the fact. Regulators and auditors typically expect you to demonstrate:
- The basis for disclosures and decisions
- Traceable document history for key transaction artifacts
- Controlled access to sensitive information
- Evidence that document handling followed internal policy and legal expectations
For teams operating under SEBI-related processes and other global due diligence standards, the practical implication is clear. Your process should show which document version was current at the time of review and how updates were governed.
Risks of poor version control: compliance gaps and deal delays
Poor version control causes two kinds of failures.
First, compliance gaps: you cannot prove whether a change was authorized, reconstruct the timeline of revisions, or show who accessed sensitive drafts.
Second, deal delays: reviewers comment on the wrong version, Q&A threads reference outdated attachments, and partners re-review documents because they’re unsure what changed.
The fix isn’t more emails or meetings. It’s enforceable rules plus a system that supports document control and audit logs.
10 enforceable naming and versioning rules partners can agree on
These rules are written so they can be enforced across law firms, bankers, auditors, consultants, and internal teams (without relying on individual memory). Each rule includes a partner enforcement angle: what you can require, not just recommend.
Rule 1: Standardize file naming format with essential metadata
Agree on one file naming format for the entire deal room and require every uploader to follow it. A practical baseline includes: deal or project identifier, document type, entity or workstream, date (in a sortable format like YYYY-MM-DD), version number, and owner or author initials.
Consistency improves search, sorting, and handoffs. Especially when documents are exported for records management.
Rule 2: Adopt uniform semantic versioning conventions
Semantic versioning translates well to due diligence documents when you define what “major” and “minor” mean.
Partner-enforceable approach: use vMAJOR.MINOR for working drafts (example: v2.3). Increment MAJOR for material changes that affect meaning, obligations, or disclosures. Increment MINOR for non-material edits such as formatting, typos, or clarifications.
The key? Every partner applies the same meaning so reviewers can immediately interpret the impact of an update.
Rule 3: Use consistent increment indicators
Teams often mix date-based versions, “final_final,” and numeric revisions. Pick one method and enforce it.
Two common approaches: numeric increments (v1.0, v1.1, v1.2, v2.0) or date plus numeric (YYYY-MM-DD_v1.0). If you use dates, standardize the format so it sorts correctly. If you use numeric increments, require that version numbers only move forward.
Rule 4: Label redacted vs. revised documents clearly
Redaction is not the same as revision. A redacted version may have the same underlying content but with masked information for a specific audience. If you don’t label this cleanly, teams can accidentally rely on a redacted copy for substantive review (or worse, distribute an unredacted copy unintentionally).
Partner-enforceable labeling rule: include an explicit label such as REDACTED or UNREDACTED in the filename. Treat redaction status as a controlled attribute, not an informal note.
Rule 5: Record version author and change summary
Review speed improves when reviewers can tell what changed without opening multiple files. Enforce one of these options: include editor initials plus a short change tag in the file name, or record the change summary in the document’s metadata field if your document management system or VDR supports it.
Keep change summaries short and factual. For example “pricing update,” “legal clause revised,” or “FY24 numbers refreshed.”
Rule 6: Never overwrite immutable archived versions
Partners should agree that “final” is a protected state.
Enforcement requirements: final or executed documents are stored as read-only, archived versions are never replaced with a new file of the same name, and if an error is found in a final, the correction is issued as a new version with a clear superseding label.
This preserves defensibility. In an audit or dispute, you want to show the sequence (not a “cleaned up” history).
Rule 7: Synchronize version control policies across all partner platforms
Version rules fail when each party applies them only inside their own tools. Your transaction needs a shared, cross-organization standard.
Practical enforcement: add the naming and versioning rules to the engagement kickoff pack, require partner confirmation before they receive upload rights, and publish a single-page “deal room naming convention” inside the data room.
Rule 8: Integrate version control with virtual data room features
Rules are stronger when the platform reinforces them. A VDR can support enforcement through role-based permissions to limit who can upload, replace, or delete files; audit trails that capture views, downloads, and uploads with timestamps; watermarking and digital rights management to discourage misuse of unauthorized versions; and version control features that preserve prior iterations instead of overwriting.
When versioning rules live inside a secure repository, you reduce side-channel sharing and increase the reliability of the document record.
Rule 9: Establish governance roles for ongoing compliance
Multi-party due diligence needs governance. Not just guidelines.
Define clear roles such as: document owner for each folder/workstream, version controller (often the deal PMO or VDR administrator) who checks compliance, and escalation point (legal/compliance lead) for conflicts and exceptions.
Governance makes rules enforceable. Without named accountability, version control becomes “everyone’s job,” which means no one’s job.
Rule 10: Audit and report on version control adherence regularly
Don’t wait for a problem to discover your process drifted. Implement a routine audit cadence: weekly naming compliance checks for new uploads, spot checks on high-risk folders (legal agreements, financial statements, regulatory drafts), and review of activity logs to confirm that only authorized users made updates.
This can be light-touch but consistent. The intent is early detection, which makes corrections easier.
How to enforce version control rules among dispersed partners
Rules alone don’t change behavior across organizations. Enforcement works when you combine onboarding, system configuration, and fast resolution paths.
Partner training and onboarding
Make onboarding part of the due diligence operating rhythm. Run a short kickoff session on naming and versioning expectations, share a one-page reference guide with examples, and require confirmation of the rules before granting upload rights.
This is pretty important when teams span legal, finance, compliance, and external advisors who may have different norms.
Leverage virtual data room automation to minimize manual errors
The most effective enforcement is making the right thing easy. Use VDR configuration to reduce manual mistakes: limit upload and edit rights to defined roles, use structured folders aligned to transaction workstreams, rely on audit logs for objective history tracking, and apply watermarking and DRM where appropriate.
If your VDR includes AI-powered indexing or metadata search, it can also reduce time wasted hunting for the correct iteration (especially when document volume is high).
Set communication and escalation protocols for version conflicts
Version conflicts will happen. Set a protocol that covers: where to flag a suspected wrong version, who decides which version is authoritative, how to mark a superseded version without deleting history, and how to notify stakeholders that a new version is now current.
Fast escalation prevents “silent divergence,” where different parties work from different versions without realizing it.
How version control aligns with cybersecurity frameworks and regulatory compliance
Version control is also a security control. It supports data integrity and reduces the chance that sensitive information is mishandled during a chaotic transaction phase.
Mapping NIST Cybersecurity Framework functions to version control
The NIST Cybersecurity Framework provides a useful way to think about controls.
Protect: Use access control, role-based permissions, encryption, and DRM to prevent unauthorized changes and sharing.
Detect: Use activity logs and change logs to spot unusual behavior, unexpected downloads, or unauthorized uploads.
Respond: Use escalation protocols to contain issues, correct document histories, and document corrective actions when something goes wrong.
This mapping keeps version control tied to risk management.
How to ensure data integrity and secure access during versioning
To keep versioning secure and defensible, partners should align on baseline safeguards: least-privilege user rights (only the necessary people can upload or modify), multi-factor authentication for user access, encrypted storage and transmission, and tamper-resistant audit trails that capture user actions.
These controls matter because a version history that can be altered or is incomplete won’t hold up under scrutiny.
What business impact does effective version control create?
Version control looks like process, but the payoff is operational. Faster reviews, fewer disputes, and higher confidence in what’s been shared and approved.
Reduction of versioning errors and compliance failures
When rules are enforced, teams typically see fewer preventable issues such as duplicate “final” documents, incorrect attachments referenced in Q&A, and time lost reconciling edits across multiple stakeholders.
You may not measure this as a single KPI, but you’ll feel it as fewer fire drills.
Streamlining document review and Q&A workflows
Consistent naming and versioning speeds review because reviewers can find documents quickly through sorting and search, comments map to a specific version reducing rework, and stakeholders spend more time reviewing substance and less time validating file accuracy.
Building stakeholder and regulator confidence
Transparent versioning and audit trails increase confidence for counterparties who need trust in document completeness, internal decision makers approving disclosures, and regulators and auditors reviewing the process later.
Confidence influences how quickly questions get resolved and whether the process is viewed as controlled and reliable.
Resources to support version control implementation
To make the rules usable across partners, package them into simple assets that can be shared at kickoff and referenced throughout the deal.
Downloadable “10 naming and versioning rules enforcement checklist”
Create a one-page checklist partners can keep open during uploads. It should include the exact file naming format with examples, the chosen semantic versioning rules, redacted/unredacted labeling requirements, “final” archiving rules, and the escalation contact for version conflicts.
Partner version control governance framework diagram
A simple governance diagram should show who owns each folder/workstream, who can upload, replace, or approve, who audits compliance, and how exceptions and conflicts are escalated and resolved.
Recommended virtual data room features for version control enforcement
When selecting or configuring a VDR to support document versioning and document control, prioritize features that reinforce enforcement: granular role-based permissions at folder and file level, comprehensive audit trails and exportable activity logs, built-in version control that preserves prior iterations, watermarking and DRM to discourage misuse of unauthorized versions, secure Q&A and notifications to keep decisions tied to the right files, and strong search and indexing to quickly locate the authoritative version.
FAQ
What are the 10 enforceable naming and versioning rules partners should apply during due diligence?
The 10 rules are: standardize file naming with essential metadata, adopt uniform semantic versioning conventions, use consistent increment indicators, label redacted vs. revised documents clearly, record version author and change summary, ensure immutable archived versions, synchronize policies across all partner platforms, integrate with VDR features, establish governance roles, and implement regular auditing and reporting.
How can partners ensure consistent version control across multiple organizations and geographic locations?
Use a shared naming and versioning agreement at kickoff, restrict upload rights until partners confirm the rules, centralize work inside a secure repository (VDR), and run recurring compliance checks using audit trails and spot audits on critical folders.
What virtual data room features help enforce version control policies automatically?
The most helpful features are role-based permissions, audit trails and activity logs, built-in version control, structured folder permissions, watermarking, DRM controls, and automated notifications tied to uploads and updates.
How do version control rules support audit readiness and regulatory compliance like SEBI ICDR guidelines?
They make it easier to demonstrate traceable document history, controlled access, and a reliable record of what was shared and relied upon at each stage. Key components of legal readiness and regulatory adherence in due diligence workflows.
How can version control policies align with cybersecurity frameworks like NIST CSF for better risk management?
Map controls to NIST functions: Protect with access control and encryption, Detect with audit logs and monitoring, and Respond with defined escalation and remediation steps when version conflicts or unauthorized actions occur.
What common mistakes should partners avoid in document versioning during high-stakes transactions?
Avoid “final_final” naming, mixing redacted and revised copies without labels, allowing overwrites of archived versions, letting too many users upload/replace files, and handling critical edits through email attachments outside the primary deal room.
How do you handle versioning for documents that undergo redactions or metadata changes?
Treat redaction as a distinct labeled variant (REDACTED/UNREDACTED) and require consistent version numbering for content changes. Track metadata changes through the system’s history tracking and audit logs where possible, so you can show what changed and when (even if document text did not).
Ready to secure your transactions?
Book a free demo of DCirrus Virtual Data Room today and experience enterprise-grade data protection with encryption, access controls, and compliance-ready localization.
Latest Posts