An Audit-Readiness Maturity Ladder for Merchant Bankers: 5 Levels From Ad Hoc Sharing to Regulator-Defensible
Audit readiness in merchant banking isn’t just about “having the documents.” It’s about proving – quickly and consistently – who shared what, with whom, when, under what controls, and why those controls were reasonable for a regulated transaction.
If you’re running IPOs, M&A, fundraising or other high-stakes mandates, you know the reality. Multiple stakeholders, tight deadlines, sensitive disclosures, and regulator scrutiny. In that environment, audit preparedness becomes an operating capability, not a last-week scramble.
This article lays out a practical audit-readiness maturity ladder built for SEBI-registered merchant bankers. It helps you self-assess your current stage, understand what “good” looks like at each level, and map the path from informal sharing to regulator-defensible compliance.
What does audit readiness actually mean in merchant banking?
In merchant banking, audit readiness (also called audit preparedness, audit compliance or regulatory readiness) is your firm’s ability to:
- Maintain complete, consistent and retrievable records of diligence activities
- Demonstrate governance, approvals and oversight around document handling
- Control access to sensitive information across internal teams and external parties
- Produce defensible evidence trails during reviews, inspections or disputes
Why it matters:
Regulatory risk – Incomplete audit trails or weak controls create avoidable queries and follow-ups.
Operational risk – Email threads, local folders and “final_v7” files lead to version conflicts and missed items.
Stakeholder risk – Investors, legal counsel, auditors and issuers lose confidence when evidence is scattered.
Deal execution pressure – Delays caused by searching for approvals, prior versions or access logs.
At higher maturity, audit readiness becomes a repeatable system: standardized workflows plus strong compliance management plus secure tooling, all aligned to multi-party transactions.
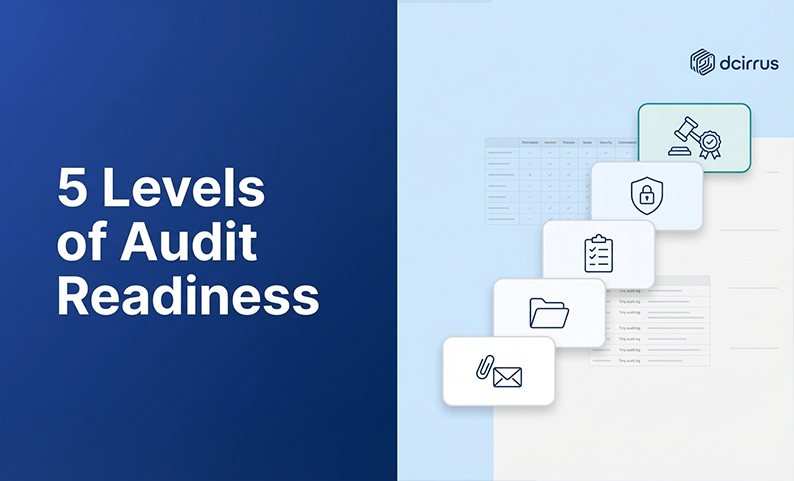
How to think about the 5 maturity levels
Each level can work “well enough” until it doesn’t. Usually at the worst time (a regulator query, a leak or a deadline crunch).
- Level 1: Ad Hoc Sharing – Unstructured collaboration, low traceability, high reliance on individuals
- Level 2: Basic Document Management – Some control but manual processes and weak audit defensibility
- Level 3: Standardized Processes with Some Technology Enablement – Defined workflows, partial automation, improved consistency
- Level 4: Integrated Secure Management with Automated Audit Trails – Strong controls, granular access, automated logs, policy-aligned operations
- Level 5: Regulator-Defensible – Continuous readiness, rapid evidence production, transparency by design, audit confidence across deals
The goal isn’t to “buy your way” to Level 5. Technology helps, but maturity is built on governance, data readiness and discipline.
Level 1: Ad Hoc Sharing – Informal, Unstructured Collaboration
What it looks like
Documents shared via email, chat apps, personal drives and generic cloud links. No consistent folder taxonomy or naming conventions. Version confusion (multiple attachments, inconsistent updates). Access decisions made informally (“just send it to them”).
What breaks first
You can’t confidently answer: Who had access to which version, and when? Reconstructing timelines from inboxes and screenshots takes time. Offboarding external users is unreliable because links keep circulating.
Typical risks
Confidentiality leakage and insider-trading exposure. Missing diligence artifacts when preparing responses. Audit trail gaps that are hard to explain across multiple stakeholders.
Level 1 is common in smaller teams. But it’s structurally fragile in regulated transactions.
Level 2: Basic Document Management – Controlled but Manual Processes
What it looks like
Shared drives or basic document portals replace “pure email.” Some versioning and access restriction, but inconsistently applied. Manual trackers (spreadsheets) record who received what. Approvals captured in emails or meeting notes rather than structured workflows.
What improves
Fewer “where is the file?” moments. Some repeatability in folder setup and internal coordination.
What still isn’t defensible
Audit evidence scattered across tools (drive, email, tracker, chat). Access logs partial, difficult to export or easy to dispute. Controls depend on people remembering steps, not systems enforcing them.
Level 2 is a step up. But most firms struggle during audits because the process is controlled in theory and manual in practice.
Level 3: Standardized Processes with Some Technology Enablement
What it looks like
Document policies exist (taxonomy, naming, retention, review cycles). Standard checklists guide diligence and IPO preparation activities. A secure data room or structured document portal is used for key workstreams. Collaboration workflows begin to centralize – commenting, Q&A, notifications.
Capabilities you start to build
Repeatable onboarding/offboarding of stakeholders. Defined roles (deal lead, compliance reviewer, uploader, approver). Partial audit trail automation, activity logs exist but not always comprehensive. Better data readiness through consistent metadata and document structure.
Where Level 3 often struggles
Teams use the platform like a “file dump” rather than a controlled workflow. Policies exist but aren’t enforced consistently. Evidence is still fragmented when a regulator asks for a full narrative.
Level 3 is where maturity begins to scale. You’re no longer improvising; you’re building a system.
Level 4: Integrated Secure Management with Automated Audit Trails
What it looks like
Secure document management integrated into day-to-day deal execution. Granular access controls applied at folder and file levels. Strong identity checks (like MFA) and device/IP restrictions. Automated audit trail logging treated as a core output, not a byproduct. Watermarking and DRM controls applied based on content sensitivity.
What becomes possible
Reliable traceability: who viewed/downloaded/printed and when. Rapid production of exportable logs and structured indexes. Clear separation of stakeholder access (issuer vs. counsel vs. auditors vs. investors). Consistent “single source of truth” for documents and communications.
At Level 4, the firm can handle complexity without losing control. Governance, controls and oversight are built into the operating model.
Level 5: Regulator-Defensible – Fully Compliant, Transparent, and Audit-Ready
What it looks like
Audit readiness is continuous, not event-based. Controls are policy-driven and consistently enforced across deals. Evidence trails are complete, exportable and understandable to outsiders. Data localization and retention practices align with regulatory expectations. Compliance management includes periodic control reviews and readiness checks.
Level 5 outputs you can reliably produce
A complete timeline of document access and diligence actions. Proof of control enforcement (permissions, DRM rules, expiry policies). Clear documentation standards and approvals aligned to internal governance. A fast, confident regulator response process without “forensic recovery.”
Level 5 is the “regulator-defensible” stage because your audit posture is explainable, repeatable and backed by controlled systems. Not personal memory or scattered artifacts.
What SEBI compliance expectations mean for your readiness checklist
Merchant bankers operate where regulator scrutiny extends beyond end deliverables to the process used to create them. While exact obligations vary by mandate and evolving guidance, audit readiness typically depends on demonstrating:
- Audit trails and traceability – Evidence of who accessed, changed or shared sensitive information with timestamps and identifiers
- Access controls and segregation – Role-based permissions preventing unauthorized access across parties and workstreams
- Data security controls – Encryption, secure authentication and mechanisms to reduce unauthorized distribution
- Data localization and residency – Ability to align storage location to applicable regional data protection expectations
- Retention and record-keeping discipline – Consistent retention policies so records remain available for required review windows
- Governance and oversight – Documented controls, review practices and accountability
A practical way to interpret “SEBI readiness”: can you show a regulator a clean, consistent story of diligence and information handling without reconstructing it from disconnected tools?
Matching technology to maturity (instead of the other way around)
Technology should support maturity, not mask gaps. The same tool can signal different maturity depending on how you run it.
A simple mapping:
- Level 1: Generic email + chat + personal storage = low control, low traceability
- Level 2: Shared drives + manual trackers = partial control, manual evidence
- Level 3: Secure data room introduced + standardized processes = growing consistency
- Level 4: Advanced VDR controls + automated audit trails + policy enforcement = audit-grade operations
- Level 5: Continuous monitoring + compliance-ready exports + repeatable governance = regulator-defensible posture
How Virtual Data Rooms enhance security and collaboration
A Virtual Data Room (VDR) is most valuable when it acts as the controlled document portal for the transaction. Where security, collaboration and evidence trails are centralized.
Core capabilities that typically matter for audit readiness:
- Granular permissions at folder and file levels to enforce least-privilege access
- Encryption for data at rest and in transit to reduce exposure risk
- Dynamic watermarking to discourage leakage and improve traceability
- Digital rights management (DRM) controls that limit printing/copying/sharing
- Real-time activity logs to support audit compliance and rapid reporting
- Collaboration features (Q&A, commenting, notifications) to reduce reliance on email
As you move up the maturity ladder, the VDR shifts from “a place to store documents” to “a system of record for diligence behavior.”
AI and automation: Accelerating audit trail accuracy
AI and automation can reduce manual overhead, but they also introduce governance questions. The AI Deployment Playbook reports that fewer than 1 in 4 banks transition from AI pilots to strategic execution, with 75% stuck in pilot cycles, and that 30% of GenAI projects may be abandoned after proof-of-concept by end-2025 due to unclear value and risk controls.
For audit readiness, AI is most useful when it strengthens control and consistency:
Automated categorization and smart indexing to improve findability. Metadata tagging to support normalized data and decision-grade data. Clause recognition and search to speed review across large sets. AI-assisted redaction to reduce human error in sensitive disclosures. Automated reporting outputs that reduce manual “log stitching.”
The maturity signal isn’t “we use AI.” It’s “we govern AI use, validate outputs and keep evidence trails clear.”
Where do you sit on the ladder? A self-assessment rubric
Use the checklist below to benchmark your current readiness stage. Don’t aim for perfection; aim for an honest baseline.
1) Document control and version integrity
Level 1: Versions tracked informally; updates shared via messages
Level 2: Basic versioning exists but enforcement is manual
Level 3: Standard naming/version policies used across deals
Level 4: Version control is system-supported; outdated versions clearly managed
Level 5: Version history is complete and easy to demonstrate externally
2) Access control and stakeholder segregation
Level 1: Access is broad or link-based
Level 2: Access restrictions exist but inconsistently applied
Level 3: Role-based access defined for key stakeholder groups
Level 4: Granular permissions, MFA and optional IP/device controls used
Level 5: Access is least-privilege by default with periodic reviews and documented rationale
3) Audit trail completeness
Level 1: Evidence reconstructed from email/chat
Level 2: Some logs exist but require manual consolidation
Level 3: Activity logs exist in core tools but not always complete
Level 4: Automated audit trails cover document actions and key collaboration events
Level 5: Audit trails are exportable, report-ready and consistently retained
4) Governance and compliance management
Level 1: No formal controls; reliance on individuals
Level 2: Informal rules exist; compliance checks are reactive
Level 3: Policies and roles exist; checks happen at milestones
Level 4: Controls embedded in workflows; oversight is proactive
Level 5: Continuous readiness checks, control testing and documented accountability
5) Deal execution consistency
Level 1: Every deal is run differently
Level 2: Templates exist but adoption varies
Level 3: Standard playbooks guide execution; fewer surprises
Level 4: Repeatable delivery with fewer delays caused by missing evidence
Level 5: Teams can respond rapidly to audits without disrupting deal velocity
If you’re Level 2 in access control but Level 4 in audit trails, that’s normal. The point is to identify the weakest link because audits and incidents usually find it first.
Why advancing maturity matters (and what staying stuck costs you)
Risks of staying at Levels 1-2
Higher likelihood of missing or inconsistent records during regulator queries. Longer diligence cycles caused by version confusion and manual follow-ups. Increased probability of unauthorized sharing due to weak controls. Greater operational drag on deal leads and compliance teams.
Benefits of advancing to Levels 3-5
Faster, cleaner diligence execution because information is structured and searchable. Better stakeholder engagement through transparent access control and collaboration. Stronger regulatory readiness due to consistent, exportable evidence trails. Reduced firefighting – fewer last-minute “please resend” and “which version is correct” loops.
Higher maturity reduces uncertainty and rework, which compresses timelines and improves confidence.
A stepwise roadmap to climb the ladder without breaking your stride
Use this roadmap to move up the readiness stages without overwhelming your teams.
1. Stabilize the basics (Level 1 → Level 2)
Define a standard deal folder taxonomy, naming conventions and a single location for authoritative documents.
2. Standardize the operating model (Level 2 → Level 3)
Create simple policies for uploads, approvals, versioning, stakeholder onboarding and retention. Assign clear owners for each step.
3. Introduce controlled collaboration (Level 3)
Move Q&A and key discussions into a controlled environment so decisions aren’t buried in email threads.
4. Automate audit evidence (Level 3 → Level 4)
Adopt tooling and workflows that automatically capture activity logs, access changes and document events as a default output.
5. Strengthen security posture and least privilege (Level 4)
Implement granular permissions, watermarking, DRM where appropriate and stronger authentication like MFA.
6. Operationalize continuous readiness (Level 4 → Level 5)
Add periodic access reviews, audit trail checks and “deal close” archiving routines that preserve evidence and improve repeatability.
A helpful discipline at each step is a lightweight weighted scoring approach: score improvement initiatives by regulatory risk reduction, operational impact and effort, then prioritize the highest-confidence wins.
Common pitfalls (and how to sidestep them)
Mistaking a tool for maturity
Buying a VDR won’t fix weak governance. Define policies and roles first, then configure the platform to enforce them.
Overreliance on manual trackers
Spreadsheets don’t scale across deals and stakeholders. Use them as transitional aids, not the system of record.
Inconsistent stakeholder onboarding
If every deal lead invites users differently, your access control posture is inconsistent. Standardize onboarding steps and permission templates.
Treating audit trails as “nice to have”
Audit trails should be a primary deliverable of your process. Build exports and review routines into milestones.
Skipping data readiness
Messy taxonomies and missing metadata reduce searchability and increase review time. Normalize document structure early.
Rolling out change without adoption support
People revert under deadline pressure. Keep training short, use templates and make the “right way” the easiest way.
A realistic IPO scenario: watching maturity evolve across the deal lifecycle
Consider a mid-market IPO preparation where the merchant banker coordinates the issuer, legal counsel, auditors and internal teams.
Early stage (Level 1 behavior)
The issuer sends diligence documents via email attachments. Legal sends markups in parallel. The banker’s team maintains a spreadsheet of “received items.” When a question comes in, someone searches inboxes for the latest version.
Stabilization (Level 2 behavior)
The team consolidates documents into a shared repository with a standard folder structure. Access is restricted by team but sharing still happens via links and ad hoc permissions. Audit evidence is still partially manual.
Standardization (Level 3 behavior)
The banker introduces standardized upload and review workflows and moves key workstreams into a secure data room. Q&A becomes centralized. Activity logs exist but the firm still has to reconcile some actions across tools.
Integrated control (Level 4 behavior)
Permissions are set by stakeholder role at folder and file levels. Watermarking is applied to sensitive documents. Audit trails capture views, downloads and changes. The compliance team can export logs and indexes when needed.
Regulator-defensible posture (Level 5 behavior)
The firm runs periodic access reviews, retains complete evidence trails and can respond quickly to questions like “Who had access to this draft and when?” The deal team doesn’t scramble; they generate a report.
The maturity shift isn’t about adding bureaucracy. It’s about reducing uncertainty and making the deal process resilient under scrutiny.
Why treating audit readiness as a capability (not a project) pays off
Audit readiness in merchant banking is a progression. From ad hoc sharing to regulator-defensible operations. The five levels help you diagnose where you are today and what to build next across:
Governance and oversight. Data readiness and documentation standards. Access control and stakeholder segregation. Audit trails and evidence quality. Technology enablement through secure, policy-driven workflows.
If you treat audit preparedness as a standing capability (not a one-time project), you reduce regulatory surprises and make deal execution smoother for everyone involved.
Ready to secure your transactions?
Book a free demo of DCirrus Virtual Data Room today and experience enterprise-grade data protection with encryption, access controls, and compliance-ready localization.