7 Email and Chat Habits That Break Auditability in IPO and M&A Q and A and What Auditable Communication Looks Like

IPO and M&A due diligence Q&A moves fast. But regulators, auditors, deal teams and investors often judge you on what you can prove later, not what you remember happened.
That’s where auditability comes in: your ability to show a complete, reliable audit trail of who said what, when they said it, what they referenced, who saw it and what changed along the way. In transaction Q&A, auditability is also compliance traceability and communication logging. The foundation for defensible, transparent workflows.
The problem? Everyday email and chat behaviors can quietly break auditability, especially when multiple parties are involved and timelines are tight.
Why Does Auditability Matter in IPO and M&A Q&A Communications?
In IPO and M&A Q&A, you’re not just exchanging information. You’re creating a record that may be reviewed during internal controls checks, regulatory communication and post-deal audits.
Auditability matters because it helps you:
- Demonstrate deal transparency when questions arise about disclosures, diligence completeness or who had access to what information
- Reduce compliance risk tied to SEBI regulations and transaction audit requirements (incomplete records can become a governance issue)
- Protect the integrity of the diligence process by keeping questions, answers, attachments and context linked and reviewable
- Avoid rework and delays when someone needs the “final” answer and can’t untangle multiple chat and email threads
When communication is non-auditable, teams often spend time reconstructing history. Manually assembling threads, screenshots and forwarded messages. That reconstruction is rarely complete, and it’s hard to defend under scrutiny.
7 Common Email and Chat Habits That Break Auditability in IPO and M&A Q&A
Below are seven habits that repeatedly cause audit trail gaps during due diligence Q&A (often without anyone realizing the damage until late-stage review).
Forwarding Internal and External Emails Without Controls
Forwarding feels harmless: “Loop them in,” “FYI,” “Please confirm.” But in deal workflows, uncontrolled forwarding can break auditability.
Here’s how:
- Splitting the same Q&A into multiple inboxes and versions
- Dropping key context, attachments or prior replies when people forward selectively
- Creating uncertainty about the “official” response versus informal commentary
- Expanding distribution beyond intended participants without clear access controls
The audit trail becomes a patchwork: partial email chains, missing earlier messages, inconsistent subject lines. If the question later becomes material or disputed, it’s difficult to show a single authoritative record.
Using Personal or Unauthorized Chat Apps for Deal Discussions
Fast chats are tempting, especially when senior stakeholders want quick answers. But using personal or unauthorized messaging platforms for deal discussions can undermine compliance traceability.
Why? Because:
- The organization may not control retention, exports or administrative audit logs
- User identities may be unclear or shared across devices
- Messages can be deleted or edited depending on platform settings
- External participants can be added informally without visibility or approval
Even if individuals keep “their own” records, that’s not the same as an auditable, centralized communication log for the transaction.
Taking and Sharing Screenshots of Sensitive Q&A Content
Screenshots are one of the fastest ways to destroy auditability while appearing to “keep evidence.”
When someone screenshots a question, an answer or a document excerpt and shares it, the content becomes disconnected from the original system of record. Important metadata is lost (who accessed it, from where, at what time, under what permissions). The screenshot can be forwarded endlessly with no reliable access log. It can be edited, cropped or taken out of context.
Screenshots turn structured regulatory communication into unstructured image files. Hard to search, hard to verify and hard to govern.
Copying and Pasting Q&A Text Into Non-Tracked Platforms
Copy-paste is another “quick fix” that causes long-term traceability problems.
Common examples? Moving Q&A text into personal notes apps, shared docs or spreadsheets, internal wikis, slide decks or general-purpose chat channels.
Once copied, the text often evolves. Someone cleans up language, merges two answers or adds interpretations. Without controlled versioning and logging, you lose the ability to show the original question, the approved answer, the time and author of edits, and the linkage to supporting documents.
This is how teams accidentally create “shadow versions” of diligence responses that don’t match what was formally shared.
Fragmented Multi-Threaded Email Chains and Chat Threads
Transaction Q&A rarely stays in one place. A question starts in email, gets debated in chat and ends as a revised email reply (while attachments live somewhere else).
Fragmentation breaks auditability because you can’t easily reconstruct the full reasoning or approval path. Different stakeholders see different slices of the conversation. “Final” answers may exist in multiple threads with subtle differences. Reviewers spend time chasing context instead of assessing substance.
Fragmentation also increases operational risk: teams may act on an incomplete thread, miss a key caveat or respond based on outdated information.
Late or Incomplete Email and Chat Archiving
Archiving is often treated as housekeeping, something to do near the end. But late or incomplete archiving creates audit trail gaps that are difficult to fix.
Typical failure patterns include:
- Not capturing attachments that were referenced but later moved or deleted
- Losing messages from participants who leave the organization or change devices
- Exporting “some” mailboxes but missing side discussions
- Relying on individuals to self-report what should be retained
In an audit context, late archiving can look like selective record-keeping (even if the real cause was simple process drift during a busy deal).
Ignoring Metadata and Access Control Limitations in Communication
Even when content is retained, auditability can still be weak if you can’t capture and prove key metadata.
Email and many chat tools struggle to provide a complete, transaction-grade record of strong user authentication tied to each action, consistent timestamps across time zones and devices, IP address or device-level access context, permission history (who could access something at a point in time), and a unified view of actions taken on related documents and messages.
You may have “messages,” but not the audit trail quality needed for deal transparency and transaction audit requirements.
What Does Auditable Communication Look Like in High-Stakes IPO and M&A Q&A?
Auditable communication is not just “saving messages.”
In IPO and M&A Q&A, it means the communication system creates a defensible record. One that connects participants (verified identities and roles), actions (asked, answered, viewed, downloaded, shared), time (reliable timestamps), context (linked documents, versions and approvals), and controls (permissions and access restrictions that are enforced, not optional).
Practically speaking? Auditable communication looks like centralized, controlled transaction Q&A where every exchange is logged and reviewable, without relying on memory, manual exports or stitched-together screenshots.
Key Features of Secure Q&A Collaboration Tools
When teams aim for compliant messaging and transparent workflows, they typically look for secure collaboration features such as:
- Automatic communication logging for questions, answers and related commentary
- Strong user authentication (including multi-factor authentication)
- Granular access controls by role, folder and file
- Version control so the latest answer and the history are both clear
- Document-level controls that limit copying, printing and uncontrolled sharing
- Watermarking and document tracking to discourage and trace leakage
- Retention and export options to support audits without manual reconstruction
The point is to build an environment where the audit trail is created as a byproduct of normal work, rather than something you try to reconstruct under deadline.
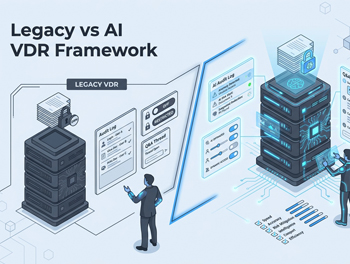
How Integrated Virtual Data Room (VDR) Q&A Forums Enhance Auditability
One practical way to reduce email and chat chaos? Shift due diligence Q&A into integrated Q&A forums within a virtual data room (VDR).
In an integrated approach, questions and answers live next to the relevant documents. Access is tied to authenticated users and defined permissions. Q&A history is centralized, searchable and consistently logged. Teams can reduce reliance on external email chains and informal chats that fragment records.
For example, a VDR platform may provide built-in Q&A discussion forums, secure messaging, document commenting, automated notifications and version control. Keeping deal-related communication inside a controlled system rather than scattered across channels.
How to Establish and Maintain Audit-Ready Communication Policies
Tools help, but policy and behavior make or break auditability. The goal is to prevent “shadow workflows” from appearing when pressure rises.
Setting Clear Policies on Communication Channels and Usage
Audit-ready policies usually clarify which communication channels are approved for transaction Q&A, what types of discussions must stay inside the auditable system (for example, diligence questions, responses and clarifications), how to handle urgent questions without moving to unauthorized apps, expectations for sharing documents and excerpts (avoiding copy-paste and screenshots), and who can invite external participants and under what approvals.
A simple, enforceable rule is better than a perfect rule nobody follows.
Training Teams and Stakeholders on Audit Compliance Risks
Most audit trail breaks aren’t malicious. They’re people optimizing for speed.
Training should help internal teams and external stakeholders understand why forwarding, screenshots and off-platform chats create compliance traceability gaps, what “good” looks like during transaction Q&A, how to use the approved system quickly (so compliance doesn’t feel like friction), and how auditability supports everyone: bankers, legal counsel, compliance officers, auditors and investors.
When stakeholders see auditability as deal protection rather than bureaucracy, adoption improves.
Leveraging Technology for Real-Time Monitoring and Immutable Audit Logs
Audit readiness improves when controls and logging are built into the workflow, such as comprehensive audit trails that track user activities, IP address restrictions and device-level approval to reduce uncontrolled access, two-factor authentication to strengthen identity verification, document tracking and dynamic watermarking with viewer details and timestamps, digital rights management (DRM) to limit printing, copying and sharing, and retention and export capabilities so audit records can be produced without last-minute scraping.
The objective is not surveillance. It’s defensibility: being able to show a reliable record of activity and communication when it matters.
What Questions Should You Ask Vendors About IPO and M&A Q&A Auditability?
If you’re assessing auditable communication tools, messaging options or VDR platforms, vendor conversations should go beyond “is it secure?” and focus on whether the platform supports end-to-end auditability for transaction Q&A.
Essential Audit Trail Features to Confirm
Ask how the vendor supports automatic timestamping of Q&A actions and document interactions, user authentication options (including multi-factor authentication), metadata capture (user identity, time, activity type and other relevant context), audit trail exportability for auditors and compliance reviews, watermarking and document tracking that ties access to identifiable users, version control for documents and any Q&A edits or updates, and controls that restrict copying, printing and uncontrolled redistribution.
You’re trying to confirm that the system doesn’t just store content. It preserves who/what/when/how in a way that stands up to scrutiny.
Compliance Standards and Integrations to Verify
Given regulatory communication needs and SEBI-facing processes, ask about alignment with transaction audit requirements and deal transparency expectations, data localization options that support regional compliance requirements, availability of recognized security certifications and audit reports, integration capabilities with existing deal workflows and data room practices, and options to export indexes or logs for structured review.
The key is whether the platform can fit into real IPO and M&A execution without forcing teams back into email and chat workarounds.
Usability and Adoption Considerations
A tool can be “compliant” on paper and still fail if people avoid it.
Evaluate how quickly internal teams and external parties can start using it. Whether Q&A is intuitive enough to replace email chains. How notifications work (so stakeholders don’t revert to chat “pings”). Mobile and cross-platform access if deal teams operate on the move. Administrative overhead for coordinators managing permissions and participants.
Usability is an auditability requirement. Poor adoption leads directly to shadow IT and fragmented communication logging.
Consequences of Poor Auditability: What Happens When the Audit Trail Breaks
When auditability breaks, the first visible symptom is often confusion: “Which answer did we confirm?” “Who approved this?” “Did the buyer’s counsel see the updated document?”
A realistic scenario looks like this: A diligence question is answered in an email thread. A revised clarification is shared later in a private chat to “save time.” Someone screenshots that clarification and forwards it to another stakeholder. Weeks later, during review, the team can’t reliably show the full chain (who asked, which version was final, who received it, what documents were referenced at the time).
The result is usually some combination of delays while teams reconstruct the record, increased legal and compliance workload to validate what happened, reduced confidence from stakeholders reviewing diligence quality, and escalations that distract senior deal leaders at critical moments.
Even when the underlying business issue is minor, the inability to prove process integrity can become a major friction point.
Accelerating Deal Timelines and Building Stakeholder Trust Through Audit-Ready Communication
Audit-ready communication isn’t only about avoiding problems. It can also make deals run cleaner by making transaction Q&A easier to manage.
Reviewers spend less time searching for context and more time evaluating substance. Deal teams reduce duplication from repeated questions and inconsistent answers. Stakeholders get confidence that the process is controlled and transparent. Compliance and audit requests are easier to satisfy because records are centralized and consistently logged.
Better audit trails support better execution (especially when multiple advisors, internal teams and external parties are collaborating under pressure).
Ready to secure your transactions?
Book a free demo of DCirrus Virtual Data Room today and experience enterprise-grade data protection with encryption, access controls, and compliance-ready localization.